Monitor API Connection status in Azure
By Anshul
- 4 minutes read - 736 wordsOverview
Hello! In this post I am going to show you how can implement a monitoring solution for your API Connections that you have used in your integrations in Azure. These API Connections allow Azure services like a logic app to connect to external services like SQL server, outlook, Sharepoint online etc.If you are not aware of these API connections, you can learn about them here.
This post is inspired from Sandro Pereira’s Blog. I have taken a slightly different approach than what has been mentioned in his blog.
Let’s get started
So, the reason we need to keep an eye on API connections is that they tend to become disconnected due to several reasons. Few of them are like if a user who authorized the connection is no longer available in AAD, or the connector fails to refresh token due to inactivity. And if something like this happens, we start to get bunch of failure notifications for all the logic apps that are using those API connections. The fix is pretty simple, you only need to reauthorize it. But to avoid all the mess and disruption that this issue could cause, is what we are trying to solve here.
So first we need a way to find out the broken/expired api connections. For that, I have used this powershell script to look for all the API connections in the subscription and then check the connection status in each of them. Here is the gist of that script
$resources | ForEach-Object {
$logicAppUrl = $_.ResourceId + '?api-version=2018-07-01-preview'
# Get Logic App Content
#$resourceJsonResult = az rest --method get --uri $logicAppUrl
$var = "https://management.azure.com" + $logicAppUrl
$accsessToken = Get-AzAccessToken `
-TenantId $connection.TenantID
$auth = "Bearer " + $accsessToken.Token
$resourceJson = Invoke-RestMethod -Uri $var -Headers @{ Authorization = $auth }
$resourceName = $_.Name
$resourceGroupName = $_.ResourceGroupName
# Check Logic App Connectors
$apiConnectionStatus = $resourceJson.properties.overallStatus
if($apiConnectionStatus -eq 'Error')
{
$apiBrokenCount++;
$apiBrokenDataNode += [pscustomobject]@{
'ResourceGroupName' = $_.ResourceGroupName;
'ResourceName' = $_.Name;
'Status' = $resourceJson.properties.statuses.status;
'APIName' = $resourceJson.properties.api.name;
'APIDisplayName' = $resourceJson.properties.api.displayName;
'ResourceType'= $resourceJson.type;
'ResourceLocation'= $resourceJson.location;
'ResourceId'= $resourceJson.id;
'ErrorCode'= $resourceJson.properties.statuses.error.code
'ErrorMessage'= $resourceJson.properties.statuses.error.message
}
}
You can download the entire script from here - Download
So as you can see, the script looks for all the connections in the subscriptions and then goes through each of them to check the connection status. If the status is marked ‘Error’, it creates a sample object with the necessry details to push forward.
Now we have the information about the broken/epired connections. Next we need a way to inform the concerned team about this so that they can take a timely action and prevent service disruption. So in order to reduce the time between something like this goes wrong and the time we get informed, I am going to use a cloud-based automation service aka Logic App and setup the mailing functionality. I can easily call an HTTP triggered Logic App from the above Powershell script using Invoke-RestMethod command.
Since we have all the services figured out, now is the time to integrate the two so that they can work together. There are two options for us as of today to run our powershell script efficiently. One can be inside Azure Functions and the other option is to run it as a Runbook in Automation Account. I personally like the automation account approach as it has been my go to option for all my powershell based automation solutions.
Steps to put the services in action
Now, you can follow these simple steps to implement the monitoring solution-
- Upload the Powershell Script as Runbook in an Automation Account
- Create a User-Assigned Managed Identity and attach it to Automation Account.
- Add this MI as Reader on the scope of your Azure Subscription (you can decide the scope based on your requirements)
- Create an HTTP-triggered Logic App and configure the Send Email action in it to send the email to respective team.
- Replace the HTTP url in the powershell script on Line 50 with the actual HTTP url of your Logic App.
- Lastly, attach a schedule to your runbook to run as per your requirement. In my case, I scheduled it to run everyday.
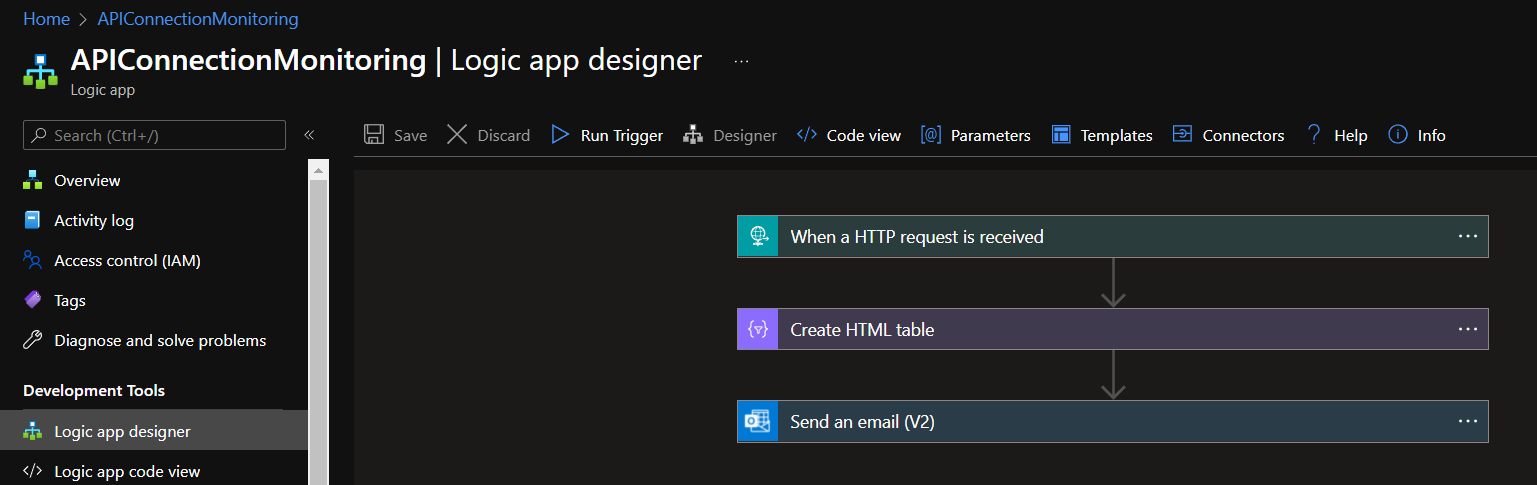
This is how my Logic App looks like
The final flow of this solution would be somthing like this-
The Runbook runs everyday---> If a broken Connection is found---> Trigger the logic app and send an email
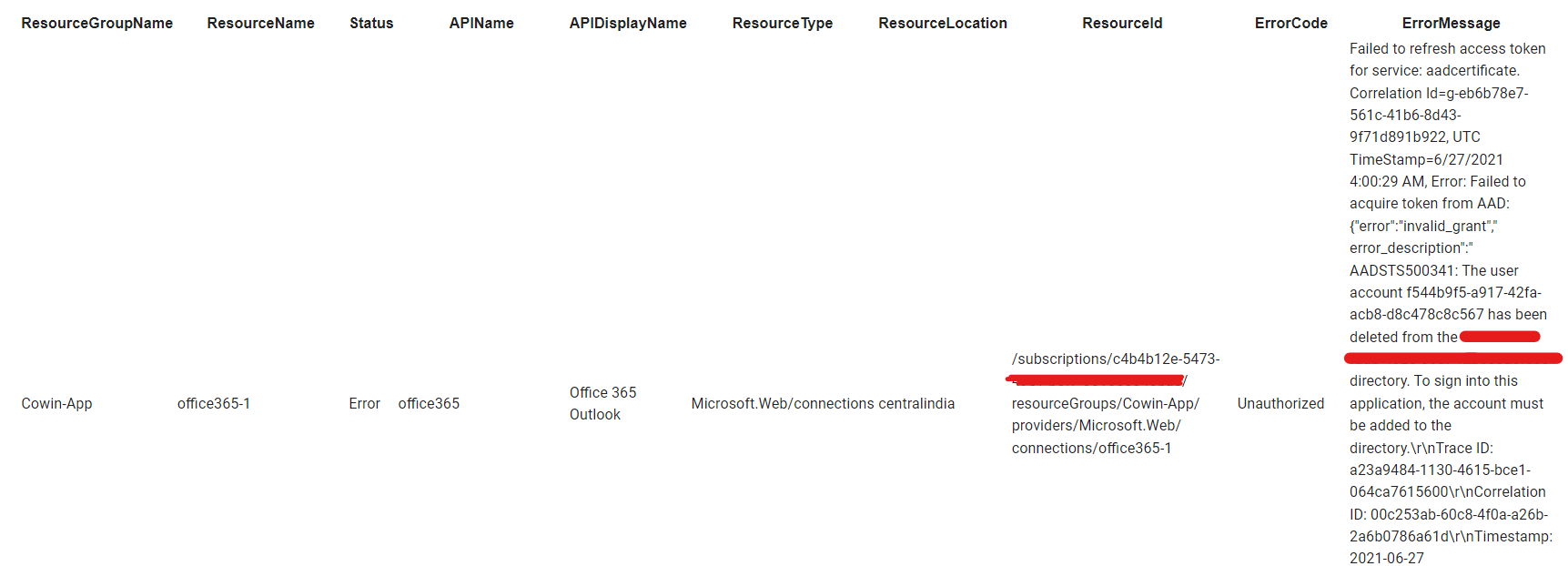
The final email in my inbox looks like this-